ZeroDay Cyber Feed
Explore fresh threat intelligence, zero-day vulnerabilities, and cyber news. Stay ahead of the curve with our real-time feed of the latest in cybersecurity.
Professional Course Tracks
Learn offensive security, network exploitation, red team operations, and real-world penetration testing techniques aligned with industry standards and hands-on vulnerability assessment practices.
Most detailed category with step-by-step breakdowns, realistic scenarios, and practical examples.
CVE posts are concise vulnerability summaries for fast awareness and prioritization.
Infrastructure assessment, exposure mapping, and internal attack-chain coverage for practical testing.
Follow CVE summaries for context, then move to Red-Team for deeper techniques and examples.
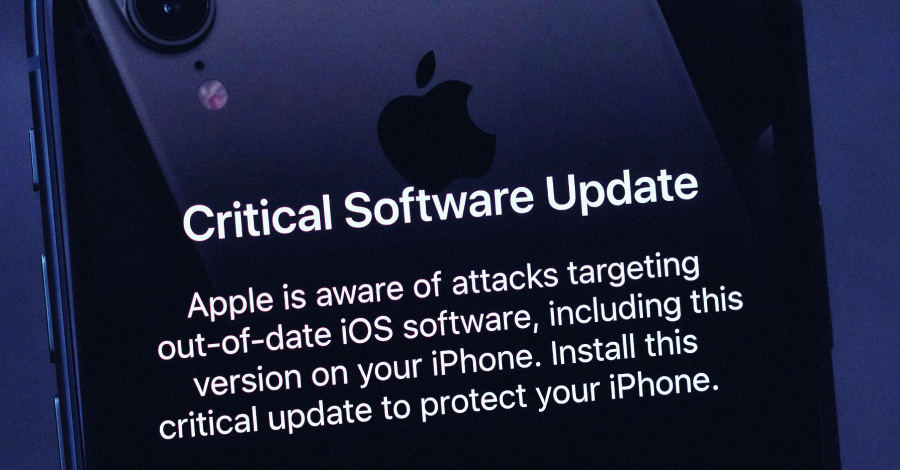
Apple is now sending Lock Screen notifications to iPhones and iPads running older versions of iOS and iPadOS to alert users of web-based attacks and urge them to install the update. The development was first reported by

TeamPCP, the threat actor behind the supply chain attack targeting Trivy , KICS , and litellm , has now compromised the telnyx Python package by pushing two malicious versions to steal sensitive data. The two versions, 4
Cybersecurity researchers have disclosed details of a now-patched bug impacting Open VSX's pre-publish scanning pipeline to cause the tool to allow a malicious Microsoft Visual Studio Code (VS Code) extension to pass the
A pro-Ukrainian group called Bearlyfy has been attributed to more than 70 cyber attacks targeting Russian companies since it first surfaced in the threat landscape in January 2025, with recent attacks leveraging a custom