ZeroDay Cyber Feed
Explore fresh threat intelligence, zero-day vulnerabilities, and cyber news. Stay ahead of the curve with our real-time feed of the latest in cybersecurity.
Professional Course Tracks
Learn offensive security, network exploitation, red team operations, and real-world penetration testing techniques aligned with industry standards and hands-on vulnerability assessment practices.
Most detailed category with step-by-step breakdowns, realistic scenarios, and practical examples.
CVE posts are concise vulnerability summaries for fast awareness and prioritization.
Infrastructure assessment, exposure mapping, and internal attack-chain coverage for practical testing.
Follow CVE summaries for context, then move to Red-Team for deeper techniques and examples.

A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. "Beyond cryptomining, the threat acto
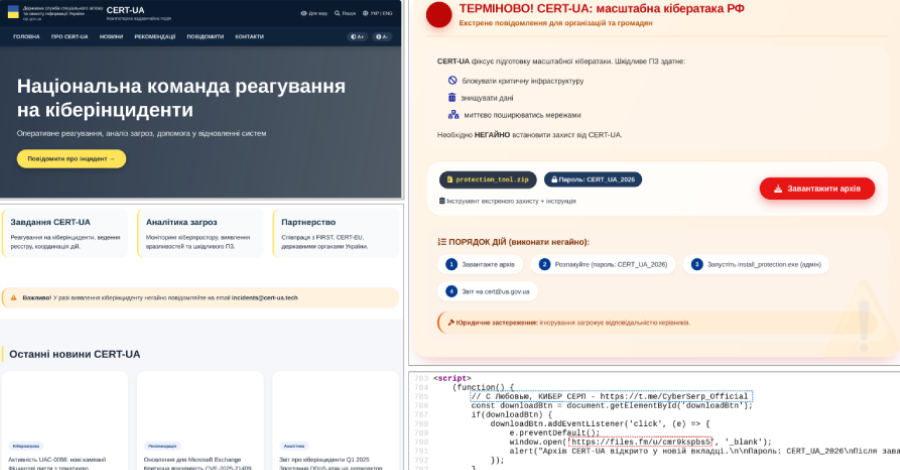
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGE

Anthropic on Tuesday confirmed that internal code for its popular artificial intelligence (AI) coding assistant, Claude Code, had been inadvertently released due to a human error. "No sensitive customer data or credentia
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281