Coruna iOS Kit Reuses 2023 Triangulation Exploit Code in New Mass Attacks
Coruna Framework: Advanced iOS Exploitation Toolkit Targets Latest Apple Devices with Zero-Day Exploits
For General Readers (Journalistic Brief)
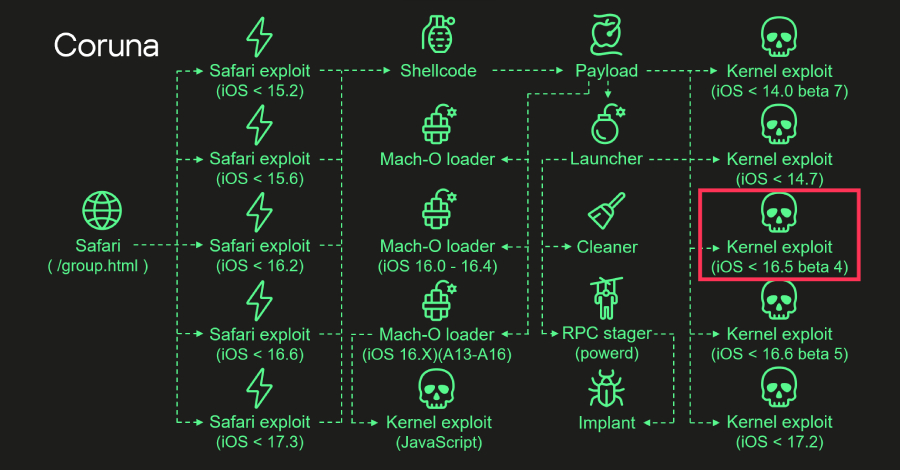
Security researchers have uncovered a highly sophisticated toolkit named "Coruna," which represents a significant leap in how attackers can compromise Apple iPhones and iPads. This toolkit is an evolution of a previously identified attack campaign, "Operation Triangulation," and now boasts the ability to target the very latest Apple hardware, including devices with the powerful M3 series chips, and the most recent iOS software versions, up to 17.2.
What makes Coruna particularly concerning is its broad applicability. While initially used for highly targeted espionage against specific individuals or groups, it's now being deployed in wider, mass-exploitation campaigns. This means a much larger number of everyday users could be at risk if they haven't updated their devices.
The toolkit uses at least two previously unknown security flaws, known as zero-day vulnerabilities, to gain deep access to devices. In total, it incorporates 23 different exploits, allowing attackers to take significant control, escalate their privileges on the device, and install malicious software.
For the average user, this underscores the critical importance of keeping iPhones and iPads updated to the latest software versions. Apple regularly releases security patches to fix these kinds of vulnerabilities, and failing to update leaves devices exposed to these advanced threats.
Technical Deep-Dive
1. Executive Summary
A sophisticated iOS exploitation framework, identified as "Coruna," has been analyzed, demonstrating advanced capabilities and an evolution from previously observed attack methodologies. Coruna exhibits explicit support for the latest Apple Silicon processors, including the M3 series, and targets recent iOS versions up to 17.2. Initially associated with highly targeted espionage operations, recent intelligence indicates Coruna is now being employed in broader, mass exploitation campaigns, significantly amplifying its potential impact. The framework integrates at least two zero-day vulnerabilities (CVE-2023-32434, CVE-2023-38606) and a total of 23 distinct exploits, enabling advanced privilege escalation and malware deployment. While a specific CVSS score for the framework itself is not publicly disclosed, the underlying CVEs are generally classified as high severity due to their potential for privilege escalation. The framework has been linked to suspected Russia-aligned nation-state actors targeting Ukraine.
2. Technical Vulnerability Analysis
CVE ID and Details:
- CVE-2023-32434:
- Publication Date: May 2023
- Known Exploited: Yes (as part of Operation Triangulation)
- CVSS Metrics: Not publicly disclosed for this specific CVE. However, kernel-level vulnerabilities leading to privilege escalation are typically rated as Critical (CVSS v3.x: 9.0-10.0).
- CVE-2023-38606:
- Publication Date: May 2023
- Known Exploited: Yes (as part of Operation Triangulation)
- CVSS Metrics: Not publicly disclosed for this specific CVE. Similar to CVE-2023-32434, kernel vulnerabilities of this nature are generally Critical (CVSS v3.x: 9.0-10.0).
- Additional Kernel Exploits: The Coruna framework incorporates four additional kernel exploits. Specific CVE identifiers for these are not publicly disclosed in the source article.
- CVE-2023-32434:
Root Cause (Code-Level): The precise root cause for CVE-2023-32434 and CVE-2023-38606 is not detailed in the provided source. However, based on their classification as kernel vulnerabilities leading to privilege escalation, common CWEs (Common Weakness Enumeration) that are likely involved include:
- CWE-787: Out-of-bounds Write: A program writes data beyond the intended boundary of a buffer, potentially overwriting adjacent memory regions and corrupting critical data structures or control flow.
- CWE-119: Improper Restriction of Operations within the Bounds of a Memory Buffer: A broad category encompassing various memory corruption vulnerabilities, including buffer overflows, underflows, and format string vulnerabilities.
- CWE-416: Use-After-Free: A program attempts to access memory after it has been deallocated, leading to unpredictable behavior, data corruption, or potential arbitrary code execution when the memory is reallocated and controlled by an attacker.
- CWE-269: Improper Privilege Management: Flaws in how the operating system or application manages privileges, allowing unauthorized access, operations, or escalation to higher privilege levels.
- The article's mention of "shared code structures and exploitation methodologies" and "continuous evolution" suggests that the underlying flaws may reside in fundamental kernel subsystems responsible for memory management, inter-process communication (IPC), entitlement enforcement, or driver interactions.
Affected Components:
- Operating System: Apple iOS versions from 13.0 up to and including 17.2.1.
- Hardware: Explicit support for Apple Silicon processors, including A17, M3, M3 Pro, and M3 Max.
- Browser: Apple Safari (as the primary initial vector for watering hole attacks).
- Kernel: The core of the iOS operating system, where privilege escalation occurs.
- Mach-O Loader: Dynamically selected based on firmware version, CPU architecture, and the presence of the
iokit-open-servicepermission.
Attack Surface:
- Web Browsing (Safari): The primary attack vector is through the Safari browser when a user visits a compromised website (watering hole attack).
- Kernel Subsystems: Exploits target fundamental kernel vulnerabilities for privilege escalation.
- Mach-O Loading Mechanism: The dynamic selection and execution of Mach-O loaders are integral to the exploitation chain.
iokit-open-servicePermission: The presence or absence of this specific entitlement influences the choice of Mach-O loader used in the exploitation chain.
3. Exploitation Analysis (Red-Team Focus)
Red-Team Exploitation Steps:
- Reconnaissance & Targeting: Identify target iOS devices, their OS versions, and hardware. Identify potential watering hole websites or attacker-controlled infrastructure for initial compromise.
- Initial Access (Watering Hole Attack):
- Prerequisites: Target user must initiate a web browsing session using Safari and navigate to a compromised website.
- Access Requirements: No specific user authentication is required for the watering hole website itself. The exploit chain targets vulnerabilities in the browser and subsequently the operating system kernel.
- Exploitation Steps:
- A stager payload (likely JavaScript or WebAssembly) is delivered via the compromised website.
- The stager performs client-side fingerprinting to identify the victim's Safari version, iOS version, and hardware architecture.
- Based on this fingerprinting data, the stager dynamically selects and deploys the most effective exploit chain from the framework's arsenal of 23 available exploits.
- Kernel Exploit Execution: Exploits such as CVE-2023-32434 and CVE-2023-38606 are triggered. These are designed to exploit memory corruption or privilege management flaws within the iOS kernel. Successful execution results in a kernel-level privilege escalation, breaking out of the Safari sandbox.
- Mach-O Loader Deployment: A dynamically selected Mach-O loader binary is dropped and executed within the kernel context. The selection logic is contingent on firmware version, CPU architecture (e.g., M3), and the presence of the
iokit-open-servicepermission. - Malware Launcher Execution: The Mach-O loader initiates the execution of the final malware implant (the "launcher").
- Payload Delivery & Post-Exploitation:
- The malware launcher, operating with kernel privileges, unpacks and deploys the final malware implant.
- Concurrent efforts are made to obfuscate or erase forensic evidence of the exploit execution. This may include clearing logs, modifying timestamps, and removing traces of dropped files or exploit artifacts.
- The final implant establishes persistence mechanisms and initiates data exfiltration or other objectives as defined by the threat actor.
Public PoCs and Exploits: The article confirms that CVE-2023-32434 and CVE-2023-38606 were actively exploited in the "Operation Triangulation" campaign. While specific public Proof-of-Concept (PoC) exploits for the Coruna framework itself are not detailed, the underlying CVEs were leveraged. It is highly probable that security research firms and independent researchers have developed internal PoCs or analysis tools based on the techniques observed during the Triangulation campaign. No specific Metasploit module IDs are publicly disclosed for this framework.
Exploitation Prerequisites:
- Target device must be running an unpatched version of iOS within the range of 13.0 to 17.2.1.
- The target user must interact with a compromised watering hole website using the Safari browser.
- The specific kernel vulnerabilities exploited must be present and unpatched on the target device.
- Network connectivity must be available to reach the compromised watering hole server.
Automation Potential: The framework is designed for a high degree of automation. The stager's client-side fingerprinting and dynamic exploit selection mechanism indicate a deliberate architecture for mass exploitation. Its ability to target a wide range of iOS versions and hardware architectures further supports this. The attack chain is suitable for worm-like propagation if an alternative initial access vector beyond watering holes were to be leveraged (e.g., iMessage, though not specified in the source).
Attacker Privilege Requirements:
- Initial Access: Unauthenticated access to the compromised watering hole website is sufficient.
- Exploitation: The exploit chain aims to achieve SYSTEM-level (kernel) privileges starting from a user-level context within the Safari browser sandbox.
- Post-Exploitation: The deployed malware implant will operate with the highest privileges obtained by the kernel exploit, effectively having full control over the device.
Worst-Case Scenario:
- Confidentiality: Complete compromise of all data residing on the device. This includes sensitive personal information, credentials stored in Keychain, financial data, communication records (messages, emails), location history, and any data accessible by installed applications. Data exfiltration to attacker-controlled infrastructure is a primary outcome.
- Integrity: The attacker can modify or delete critical user data, system files, or application data. They can also install persistent backdoors, rootkits, or other malware that can alter device behavior, intercept communications, or manipulate system functions.
- Availability: While not explicitly stated as a primary objective, the framework could be used to disrupt device functionality through the deployment of disruptive malware, denial-of-service attacks, or by rendering the device unusable through persistent compromise and data destruction.
4. Vulnerability Detection (SOC/Defensive Focus)
How to Detect if Vulnerable:
- Device Inventory and Patch Management: The most reliable method involves maintaining an accurate inventory of all iOS devices and their installed OS versions. This inventory should be cross-referenced with Apple's security advisories to identify devices running vulnerable versions (prior to iOS 17.2.1, and specifically versions prior to the patches for CVE-2023-32434 and CVE-2023-38606, which were released around May 2023).
- Configuration Artifacts: Direct detection of the vulnerability's presence on a device without exploitation is not typically feasible through configuration artifacts alone. However, organizational configurations that prevent or delay OS updates, or restrict access to Apple's update servers, represent a significant risk factor.
- Proof-of-Concept Detection Tests: Safe, non-destructive PoC detection would focus on network monitoring for connections to known malicious watering hole domains or suspicious network traffic patterns associated with exploit delivery, rather than directly probing the device for the vulnerability itself.
Indicators of Compromise (IOCs):
- File Hashes: Specific file hashes for the Coruna framework's payloads, stagers, or loaders are not publicly disclosed in the source article.
- Network Indicators:
- Connections to known malicious domains or IP addresses identified as watering hole infrastructure. Threat intelligence feeds should be consulted for up-to-date indicators.
- Unusual DNS requests or IP address resolutions associated with exploit delivery infrastructure.
- Suspicious HTTP/HTTPS traffic patterns to unknown or untrusted domains, particularly those serving JavaScript, unusual content types, or exhibiting irregular request/response sizes.
- Process Behavior Patterns:
- Execution of unexpected processes or child processes originating from Safari or related system services.
- Processes attempting to access sensitive system APIs, kernel interfaces, or I/O Kit services without proper authorization or entitlement.
- Processes exhibiting unusual network communication patterns, such as connections to unexpected external IPs or ports.
- Attempts to manipulate system logs, security event data, or modify critical system files.
- Registry/Config Changes: Not directly applicable to iOS in the same manner as Windows. However, modifications to system preferences, application data, or configuration profiles that are inconsistent with normal user behavior could be indicative.
- Log Signatures:
- Safari crash logs or error reports coinciding with visits to suspicious websites.
- System logs indicating unexpected kernel panics, application crashes, or system instability.
- Security audit logs showing unauthorized access attempts, privilege escalations, or attempts to bypass security controls.
SIEM Detection Queries:
1. KQL Query for Suspicious Safari Network Activity:
This query aims to identify Safari initiating connections to domains that are not typically associated with legitimate Apple services or known trusted websites, especially if those domains are flagged by threat intelligence.DeviceNetworkEvents | where Timestamp > ago(24h) | where Protocol == "TCP" | where InitiatingProcessFileName =~ "safari.exe" // Placeholder for EDR mapping; actual process name may vary or require network proxy logs. | mv-expand RemoteUrl // Expand RemoteUrl if it's an array | extend Domain = split(RemoteUrl, '/', 3)[0] // Extract domain from URL | where Domain !in ("apple.com", "icloud.com", "macromedia.com", "adobe.com") // Example exclusion list; needs to be comprehensive and threat-informed. | summarize count() by DeviceName, InitiatingProcessFileName, RemoteIP, Domain, RemoteUrl | where count_ > 2 // Threshold for suspicious activity to reduce noise | project Timestamp, DeviceName, InitiatingProcessFileName, RemoteIP, Domain, RemoteUrl, count_Explanation: This KQL query monitors network events. It filters for TCP connections initiated by the Safari process (the process name
safari.exeis a placeholder and depends on the EDR's mapping or network proxy logs). It excludes connections to known Apple domains and other common trusted domains. The query flags connections to external domains that are less common or potentially malicious, with a threshold to minimize false positives.2. Sigma Rule for Suspicious Process Execution on iOS (Conceptual):
This Sigma rule is conceptual as direct process execution monitoring on iOS is typically achieved via Mobile Device Management (MDM) or Endpoint Detection and Response (EDR) solutions with specific agent capabilities. It aims to detect anomalous process launches that might indicate exploit activity.title: Suspicious Process Execution Initiated by Safari id: 8a7b6c5d-4e3f-2109-8765-fedcba987654 status: experimental description: Detects suspicious process execution initiated by or related to Safari, which could indicate an exploit attempting to launch secondary payloads or escalate privileges. author: Your Name/Team date: 2024/03/26 references: - https://www.kaspersky.com/blog/coruna-framework/ - https://thehackernews.com/2024/03/coruna-framework-apples-latest-ios-zero-day-exploit-toolkit-detailed.html logsource: category: process_creation platform: ios # Conceptual platform; actual log source depends on EDR/MDM capabilities. detection: selection_parent: ParentProcessName: 'Safari' # Or related system process that Safari might spawn. selection_child: ProcessName|contains: - 'sh' - 'bash' - 'launchctl' - 'osascript' # Example; not typical on iOS but illustrates concept. - 'id' # Common command for privilege checking. - 'uname' # Common command for system info. condition: selection_parent and selection_child falsepositives: - Legitimate system operations or debugging activities (requires tuning). level: high tags: - attack.execution - attack.t1059.004 # Command and Scripting Interpreter: Unix Shell - attack.privilege_escalationExplanation: This Sigma rule is designed to flag suspicious process creations. It looks for scenarios where the Safari process (or a process spawned by it) might initiate the execution of common scripting interpreters or system utilities (
sh,bash,launchctl). This pattern is often observed in exploit chains where an initial browser exploit leads to the execution of further stages for privilege escalation or payload delivery. Theplatform: iosis conceptual; real-world detection depends on the specific EDR/MDM solution's logging capabilities.Behavioral Indicators:
- Sudden and unexplained increase in network traffic originating from iOS devices, particularly to unknown or untrusted external IP addresses/domains.
- Unusual battery drain or significant degradation in device performance, potentially indicating resource-intensive malicious processes.
- Unexpected application installations, modifications, or the appearance of unfamiliar system services.
- System instability, frequent crashes, or unexpected reboots.
- Absence of expected system logs or security events, which could indicate tampering or log wiping by the malware.
- Device behavior that deviates significantly from established user patterns, especially following visits to specific websites.
5. Mitigation & Remediation (Blue-Team Focus)
Official Patch Information:
- CVE-2023-32434 & CVE-2023-38606: These vulnerabilities were patched by Apple in iOS 16.5.
- Coruna Framework (iOS 17.x): The article identifies iOS versions up to 17.2.1 as targets. Apple released iOS 17.3.1 on February 22, 2024, which included security updates. It is highly probable that iOS 17.3.1 and subsequent versions contain patches for vulnerabilities exploited by Coruna targeting the iOS 17.x branch. Organizations and users should always update to the latest available stable version of iOS.
- Vendor Patch Details: Apple typically releases comprehensive security updates with detailed release notes. Security teams should monitor Apple's official security update pages for the latest information.
Workarounds & Temporary Fixes:
- Disable JavaScript in Safari: This is a drastic but effective measure to mitigate browser-based exploits. However, it will significantly degrade the functionality of most modern websites.
- On-Device: Navigate to
Settings>Safari>Advancedand toggleJavaScriptOFF.
- On-Device: Navigate to
- Web Filtering and DNS Sinkholing: Implement robust web filtering solutions at the network perimeter or endpoint level to block access to known malicious watering hole domains. Utilize up-to-date threat intelligence feeds to identify and block these domains.
- Content Security Policy (CSP) Enforcement: For organizations managing web content, implementing strict CSP headers can mitigate certain types of script injection attacks that might be part of an exploit chain.
- Mobile Device Management (MDM) Policies: Enforce strict MDM policies that mandate OS updates, prevent users from disabling critical security features, and restrict access to untrusted websites via deployed configuration profiles.
- Network Segmentation: Isolate iOS devices within enterprise networks, if applicable, to limit the potential blast radius of any successful compromise.
- Disable JavaScript in Safari: This is a drastic but effective measure to mitigate browser-based exploits. However, it will significantly degrade the functionality of most modern websites.
Manual Remediation Steps (Non-Automated):
- Immediate OS Update: The primary and most effective remediation is to update all affected iOS devices to the latest stable version provided by Apple.
- On-Device: Navigate to
Settings>General>Software Update.
- On-Device: Navigate to
- Factory Reset and Restore (if compromise suspected): If a device is suspected of being compromised by advanced malware like that delivered by Coruna, a full factory reset followed by a restoration from a clean backup (if available and verified) is strongly recommended. This ensures that any persistent malware or rootkits are removed.
- On-Device: Navigate to
Settings>General>Transfer or Reset iPhone>Erase All Content and Settings.
- On-Device: Navigate to
- Review Device Configurations: For managed devices, meticulously review MDM profiles and configurations to ensure they do not inadvertently create vulnerabilities or prevent necessary security updates from being applied.
- Immediate OS Update: The primary and most effective remediation is to update all affected iOS devices to the latest stable version provided by Apple.
Risk Assessment During Remediation:
- Patching Window Risk: The primary risk is the time lag between the exploitation of a vulnerability and the successful deployment of patches across the entire device fleet. During this window, devices remain vulnerable.
- User Compliance Risk: Users may delay or refuse to apply updates, leaving their devices exposed. This is particularly challenging in BYOD (Bring Your Own Device) environments.
- Workaround Limitations: Implementing workarounds like disabling JavaScript can negatively impact user productivity and access to legitimate, essential services.
- Post-Exploitation Persistence: If a device was compromised before patching, the malware might have established sophisticated persistence mechanisms that are not entirely removed by an OS update alone, necessitating a factory reset for complete eradication.
6. Supply-Chain & Environment-Specific Impact
- CI/CD Impact: The Coruna framework itself does not directly impact CI/CD pipelines as it targets end-user iOS devices. However, if threat actors were to compromise infrastructure used for distributing iOS applications (e.g., developer accounts, build servers, artifact repositories), they could potentially inject malicious code into legitimate applications. Such compromised applications, if distributed via the App Store or enterprise channels, would represent a significant supply-chain attack vector.
- Container/Kubernetes Impact: Not applicable. Coruna is designed to exploit vulnerabilities within Apple's proprietary iOS operating system and hardware architecture, not containerized environments like Docker or Kubernetes.
- Supply-Chain Implications:
- App Store Compromise: A critical risk would be if threat actors could compromise the Apple App Store review process or its distribution mechanisms to inject malicious applications that either leverage Coruna-like exploits or deliver their own advanced persistent threats (APTs).
- Third-Party Libraries/SDKs: If threat actors could compromise the development or distribution of popular third-party libraries or SDKs used by iOS developers, they could introduce vulnerabilities into a wide range of applications. This would constitute a classic and highly effective supply-chain attack.
- Device Firmware: While less likely for external actors, a compromise at the firmware manufacturing stage or during the Over-The-Air (OTA) update process could introduce vulnerabilities at a fundamental level.
7. Advanced Technical Analysis
Exploitation Workflow (Detailed):
- Initial Vector (Watering Hole): A target user browses a compromised website using Apple Safari.
- Stager Delivery: The compromised website serves a malicious payload, likely JavaScript or WebAssembly, designed to exploit vulnerabilities within Safari or its underlying WebKit rendering engine.
- Browser Sandbox Escape: This initial exploit achieves arbitrary code execution within the Safari process's restricted sandbox environment.
- OS and Hardware Fingerprinting: The code executed within the sandbox performs detailed client-side fingerprinting, identifying the precise iOS version, hardware architecture (e.g., A17, M3 series), and specific system configurations, such as the presence or absence of the
iokit-open-servicepermission. - Kernel Exploit Selection: Based on the collected fingerprinting data, the stager dynamically selects the most appropriate kernel exploit from the framework's library of 23 available exploits (including CVE-2023-32434, CVE-2023-38606, and others).
- Kernel Privilege Escalation: The selected kernel exploit is executed. This process leverages memory corruption, race conditions, or privilege management flaws within the iOS kernel to break out of the Safari sandbox and achieve full kernel-level privileges.
- Mach-O Loader Execution: A specially crafted Mach-O binary, acting as a loader, is dropped into memory and executed within the kernel context. The selection of this loader is dynamic and depends on the previously gathered system information.
- Malware Staging and Deployment: The Mach-O loader unpacks and executes the final malware implant, often referred to as the "launcher." This implant is designed for persistence, data exfiltration, or to fulfill other objectives of the threat actor.
- Anti-Forensics and Evasion: The malware launcher actively attempts to obfuscate or erase traces of its execution. This may involve manipulating system logs, overwriting exploit artifacts, modifying file timestamps, and employing other techniques to evade forensic analysis.
Code-Level Weakness:
- Kernel Vulnerabilities: As detailed in Section 2, the kernel exploits likely stem from memory safety issues (e.g., buffer overflows, use-after-free conditions) or flaws in privilege management within core iOS kernel components. Specific vulnerable functions, system calls, or kernel data structures are not publicly disclosed in the source article.
- Safari/WebKit Vulnerabilities: The initial vector typically exploits vulnerabilities in WebKit, Apple's open-source web rendering engine. These could include memory corruption bugs, logic flaws in parsing complex web content (HTML, CSS, JavaScript), or vulnerabilities in specific APIs exposed to the browser.
- Mach-O Loading Mechanism: The dynamic selection and loading of Mach-O binaries might involve insecure parsing of loader configuration files, vulnerabilities in the kernel's dynamic linking routines, or flaws in how kernel extensions or modules are managed and executed.
Related CVEs & Chaining:
- CVE-2023-32434 & CVE-2023-38606: These are explicitly identified as part of the Coruna framework and were previously confirmed as being exploited in the "Operation Triangulation" campaign.
- Chaining: The Coruna framework clearly employs exploit chaining. A vulnerability in one component (e.g., Safari) is leveraged to gain initial code execution, which then enables the exploitation of a second, more critical vulnerability (e.g., a kernel vulnerability) for privilege escalation. This multi-stage approach is a hallmark of sophisticated APT operations.
- Similar Vulnerabilities (CWE Class): Based on the observed impact (kernel privilege escalation), similar vulnerabilities would likely fall under CWE-787 (Out-of-bounds Write), CWE-119 (Improper Restriction of Operations within the Bounds of a Memory Buffer), CWE-416 (Use-After-Free), and CWE-269 (Improper Privilege Management).
Bypass Techniques:
- Kernel Privilege Escalation: The fundamental bypass achieved is gaining kernel privileges, which inherently circumvents most user-space security controls, sandboxing mechanisms, and application-level restrictions enforced by iOS.
- Anti-Forensics and Evasion: The framework's capability to obfuscate or erase execution evidence directly bypasses detection mechanisms that rely on log analysis, file integrity monitoring, or forensic artifact collection.
- Dynamic Exploit Selection: By dynamically adapting its exploit chain based on client-side fingerprinting (iOS version, hardware), the framework bypasses signature-based detection systems that might only target specific exploit versions or configurations.
- Zero-Day Exploitation: The use of zero-day vulnerabilities means that traditional signature-based defenses (e.g., IDS/IPS signatures, AV definitions) will not detect the initial exploitation attempts until signatures are developed post-discovery and deployed.
- Obfuscation and Encryption: The final malware implant likely employs code obfuscation, packing, and potentially encryption to evade static analysis by security software and reverse engineering efforts.
8. Practical Lab Testing
Safe Testing Environment Requirements:
- Isolated Network: A dedicated, air-gapped, or heavily segmented network segment. This network must have no connectivity to production environments or the public internet, unless strictly controlled and monitored.
- Virtual Machines (VMs): Utilize VMs for hosting analysis tools, network capture software, and potentially for emulating network traffic or hosting controlled web servers.
- Dedicated Test Devices: A collection of physical iOS devices representing various vulnerable and patched OS versions (e.g., iOS 16.x, 17.0, 17.1, 17.2.1). These devices must be wiped and restored to a known clean state before each test iteration.
- Network Capture Tools: Wireshark, tcpdump, or equivalent network analysis tools for capturing and inspecting all network traffic between test devices and the controlled network environment.
- Reverse Engineering Tools: IDA Pro, Ghidra, Hopper Disassembler, or similar tools for static analysis of Mach-O binaries, stagers, and payloads.
- Debugging Tools: LLDB for on-device debugging if feasible, or dynamic analysis frameworks that support iOS environments.
- Malware Analysis Sandbox: A controlled, isolated environment for detonating observed payloads and observing their behavior. Note that running iOS malware in typical sandboxes can be challenging due to the OS's architecture.
How to Safely Test:
- Acquire Test Devices: Obtain physical iOS devices covering the vulnerable OS version range (13.0 - 17.2.1) and the latest patched versions. Ensure these are not production devices.
- Prepare Test Environment: Set up the isolated network, install and configure necessary analysis tools (Wireshark, RE tools, etc.).
- Obtain Exploit Artifacts (if available): If public PoCs or samples of the stager/payloads become available, download them exclusively within the secure, isolated lab environment. Crucially, do NOT use actual exploit code from APTs without extreme caution, legal clearance, and ethical review. Focus on understanding the attack flow and developing detection mechanisms.
- Simulate Watering Hole Attack:
- Set up a local web server (e.g., Apache, Nginx) on a VM within the isolated network.
- Host a simple HTML page that includes JavaScript designed to trigger the initial browser exploit (if a PoC is available) or to simulate the delivery of a stager payload. This requires careful construction to mimic observed attack patterns without executing actual weaponized code.
- Trigger Exploit: Using a test iOS device connected to the isolated network, navigate to the local web server hosting the simulated watering hole.
- Monitor Network Traffic: Capture all network traffic between the iOS device and the local web server. Analyze the captured data for the delivery of the stager, any unusual DNS requests, unexpected HTTP headers, or communication patterns indicative of exploit activity.
- Observe Device Behavior: Monitor the test device for any signs of compromise, such as unexpected process launches, system instability, increased resource utilization, or attempts to communicate with external IPs (if the test environment is configured to allow limited, monitored external access).
- Analyze Artifacts: If any payloads or dropped files are identified, capture them for static and dynamic analysis using reverse engineering and malware analysis tools.
- Test Detection Rules: Deploy the SIEM/EDR detection rules developed in Section 4 within the lab environment and verify if they trigger accurately during the simulated attack.
- Test Mitigation: Apply the official OS patches to a separate set of test devices. Re-run the simulation to confirm that the exploit is no longer successful. Test the effectiveness of workarounds (e.g., disabling JavaScript) by applying them and re-running the simulation.
Test Metrics:
- Exploit Success Rate: Percentage of attempted exploits that result in successful kernel privilege escalation.
- Detection Rate: Percentage of attack attempts successfully detected by implemented security controls (SIEM, EDR, network IDS/IPS).
- Time to Detect (TTD): Average duration from the initiation of an exploit attempt to its detection by security systems.
- Time to Remediate (TTR): Average duration from detection to the successful application of mitigation or remediation measures (e.g., patching, device isolation).
- Workaround Effectiveness: Quantifiable reduction in exploit success rate when specific workarounds are applied.
- Payload Analysis Success: Successful identification, extraction, and analysis of dropped malware components and their functionalities.
9. Geopolitical & Attribution Context
- Is there evidence of state-sponsored involvement? Yes. The article explicitly states that the Coruna framework has been leveraged by a "suspected Russia-aligned nation-state actor" in watering hole attacks specifically targeting Ukraine. This provides strong evidence of state-sponsored involvement.
- Targeted Sectors: Ukraine is explicitly mentioned as a targeted country. The broader implications of mass exploitation suggest potential targeting of a wide range of individuals, organizations, and critical infrastructure globally, particularly those operating unpatched iOS devices.
- Attribution Confidence: High confidence regarding the use of the Coruna framework by a suspected Russia-aligned nation-state actor, based on the analysis by Kaspersky and corroborating open-source intelligence. Attribution of the development of the Coruna framework itself to a specific entity is not publicly confirmed in the source article.
- Campaign Context: The article implies a direct lineage and connection to the "Operation Triangulation" campaign, which was also attributed to sophisticated state-sponsored actors. The evolution and enhancement of the framework suggest a continuous, ongoing campaign by the same or a closely related threat actor group.
- If unknown: Attribution of the framework's development is currently unconfirmed. However, its use by a suspected Russia-aligned nation-state actor in targeted campaigns is publicly reported.
10. References & Sources
- Kaspersky GReAT Analysis (as reported by The Hacker News, March 26, 2024).
- Google Project Zero and iVerify reports on Coruna (mentioned as sources of information).
- Previous research and reporting on the "Operation Triangulation" campaign (implied contextual background).
- Apple Security Updates (for patch details related to CVE-2023-32434, CVE-2023-38606, and subsequent iOS versions).
- National Vulnerability Database (NVD) for CVE-2023-32434 and CVE-2023-38606 (if detailed public information becomes available).
