Destructive Lotus Wiper Targets Venezuelan Energy Sector
Destructive Lotus Wiper Targets Venezuelan Energy Sector
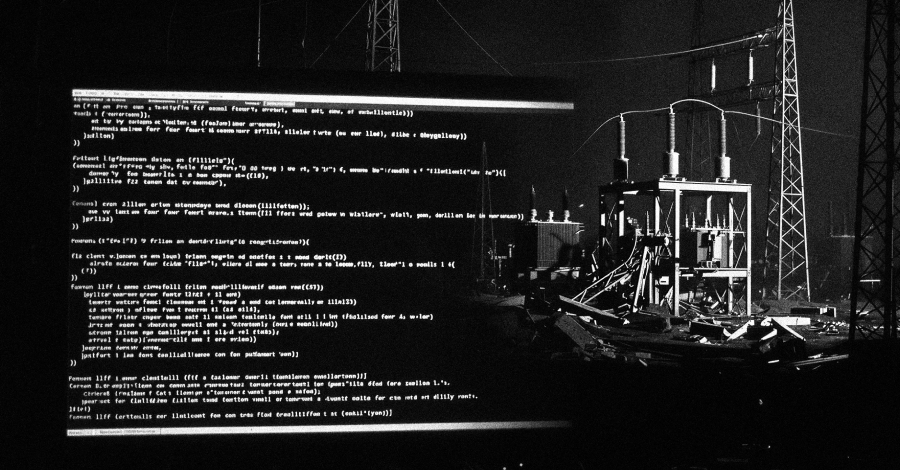
A newly identified data wiper, dubbed Lotus Wiper, has been employed in targeted attacks against Venezuela's energy and utilities infrastructure, leaving systems inoperable without any ransom demands.
Published: 2026-04-22 | Author: Patrick Mattos
Cybersecurity researchers have uncovered a sophisticated data wiper malware, named Lotus Wiper, that has been deployed in destructive campaigns against critical infrastructure in Venezuela. The attacks, which occurred in late 2025 and early 2026, specifically targeted the nation's energy and utilities sector, leaving affected systems in a state of complete inoperability. Notably, the malware's design and execution suggest a motive beyond financial gain, as it lacks any extortion or payment instructions.
The discovery, detailed by Kaspersky, highlights the potential for highly targeted destructive attacks against vital industries. The wiper's functionality, including its method of operation and its targeting of older Windows versions, suggests a deep understanding of the compromised environment by the adversaries. This raises concerns about the potential for similar attacks against other critical sectors or regions.
The attack chain involves a series of batch scripts designed to systematically dismantle defenses and prepare systems for the final payload. This process includes disabling crucial services, manipulating network configurations, and ultimately overwriting or deleting all data on affected drives. The lack of financial motivation and the specific targeting point towards a potentially state-sponsored or ideologically driven operation.
Technical Context
The Lotus Wiper attack chain commences with an initial batch script. This script's primary objective is to prepare the environment for the wiper payload by disrupting normal operations and weakening system defenses. A key action involves attempting to stop the Windows Interactive Services Detection (UI0Detect) service. This service, which is absent in modern Windows versions (post-Windows 10 version 1803), suggests the malware is designed to operate on legacy systems.
Following this, the script checks for the presence of a NETLOGON share, a common component in Windows domain environments. It then attempts to access a remote XML file. The script also performs a local check for a file with the same name within a predefined directory ("C:\lotus" or "%SystemDrive%\lotus"). This local check likely serves to ascertain if the machine is part of an Active Directory domain. If the remote file is not found, the script may introduce a randomized delay before retrying the network check.
Upon successful execution, a second batch script is initiated. This script enumerates local user accounts, disables cached logins, logs off active sessions, and deactivates network interfaces. A critical step involves executing the diskpart clean all command, which systematically wipes all identified logical drives. Furthermore, it leverages the robocopy utility to recursively mirror folders, overwriting existing content or deleting them, and uses fsutil to create files that consume all available free space, thereby exhausting storage capacity and hindering recovery efforts.
Finally, the Lotus Wiper payload is deployed. It systematically deletes restore points, overwrites physical sectors with zeros, clears the update sequence numbers (USN) of volume journals, and erases files across all mounted volumes, rendering the system inoperable. The malware's design, particularly its targeting of older Windows versions, indicates that the threat actors likely possessed prior knowledge of the target environment and had compromised the domain well in advance of the destructive attack.
Impact and Risk
The primary impact of the Lotus Wiper is the complete destruction of data and the rendering of affected systems inoperable. Organizations within the energy and utilities sector in Venezuela are directly at risk. The absence of any ransom demands suggests that the attackers' objectives are not financial, but rather focused on disruption and potentially causing significant damage to critical infrastructure. This elevates the severity of the threat, as the motivation could be geopolitical or ideological, leading to potentially widespread and sustained attacks. The targeted nature of the attack implies that specific entities within Venezuela's energy sector were deliberately chosen for disruption.
Defensive Takeaways
Organizations, particularly those in critical infrastructure sectors, should implement robust monitoring for suspicious activities. Key indicators include:
- NETLOGON Share Monitoring: Closely monitor for any unusual access or modifications to the NETLOGON share, as this is a critical component for domain operations.
- Native Utility Abuse Detection: Implement detection for the misuse of native Windows utilities such as
diskpart,robocopy, andfsutil, especially when executed in sequence or with unusual parameters. - Service Tampering: Monitor for attempts to stop or disable critical Windows services, particularly those related to system detection or user interaction.
- Endpoint Detection and Response (EDR): Ensure EDR solutions are configured to detect file deletion, overwriting, and unusual disk operations.
- System Hardening: Prioritize patching and upgrading systems to modern, supported versions of Windows to mitigate vulnerabilities exploited by malware targeting older operating systems.
- Network Segmentation: Implement strong network segmentation to limit the lateral movement of malware within the network.
- Incident Response Preparedness: Maintain up-to-date incident response plans that specifically address destructive wiper malware scenarios.
