Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
Docker Daemon Vulnerability Exposes Host Systems via Authorization Bypass
A critical security flaw in Docker Engine, identified as CVE-2026-34040, has been disclosed, presenting a significant risk to organizations relying on containerization for their applications. This vulnerability allows attackers to bypass authorization controls, potentially leading to unauthorized access and complete compromise of the underlying host systems. The flaw is an unintended consequence of an earlier security patch, highlighting the complexities of securing complex software.
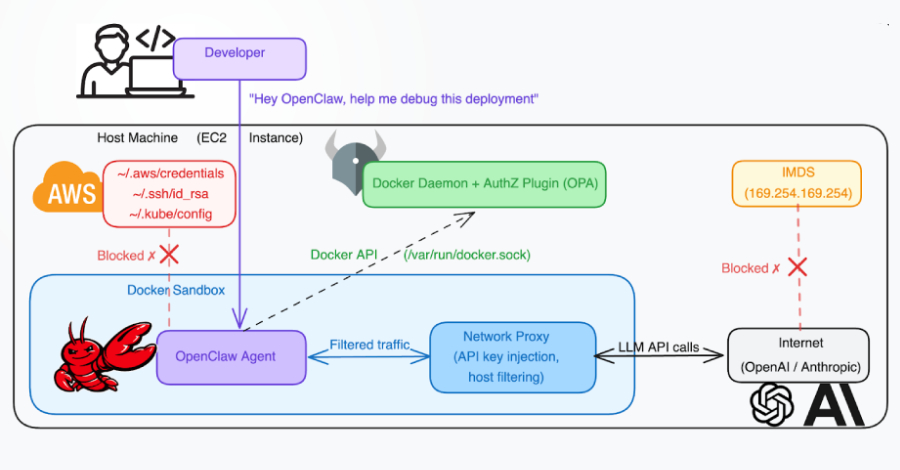
The vulnerability stems from how Docker Engine handles specially crafted API requests. When an attacker sends a malformed request with an oversized body, the Docker daemon may truncate this data before it's properly inspected by security plugins. This incomplete inspection can trick the authorization plugin into granting access, enabling the creation of a privileged container that can then access the host's file system and sensitive data.
This discovery poses a substantial threat, particularly to environments utilizing authorization plugins to govern access to Docker. The potential ramifications include data theft, such as cloud credentials and private keys, and full system takeover, which could then be leveraged for further malicious activities. Docker has released an update to address this issue, and immediate patching is strongly recommended.
Technical Context
CVE-2026-34040 is a high-severity vulnerability (CVSS score of 8.8) affecting Docker Engine. It permits an authorization bypass by exploiting an incomplete fix for a prior vulnerability, CVE-2024-41110. The core of the issue lies in the Docker daemon's handling of HTTP request bodies sent to its API.
When an attacker crafts an HTTP POST request to the Docker API, specifically targeting endpoints like /containers/create, and includes a request body that exceeds a certain size threshold (e.g., over 1MB), the Docker daemon may prematurely truncate or discard parts of this body. This occurs before the data is fully processed by any configured authorization plugins (AuthZ plugins).
Consequently, the AuthZ plugin receives an incomplete or empty request body. If the plugin's logic relies on inspecting this body for authorization decisions, it may incorrectly deem the request safe or non-malicious, thereby returning an "allow" status. The Docker daemon, having received this approval, then proceeds to execute the original request, which might include parameters for creating a privileged container with extensive host system access, such as mounting the host's root filesystem.
Likely Attack Chain Stages:
- Reconnaissance: Identify a target system running a vulnerable Docker Engine version with an active AuthZ plugin. Determine access methods to the Docker API (local user or network exposure).
- Request Crafting: Construct a malicious HTTP POST request to a Docker API endpoint (e.g.,
/containers/create). This request includes parameters for privileged container creation and host mounts, coupled with an intentionally oversized request body. - Exploitation: Transmit the crafted request to the Docker API.
- Authorization Bypass: The Docker daemon truncates the oversized request body before full inspection by the AuthZ plugin. The plugin, receiving incomplete data, erroneously authorizes the action.
- Privileged Container Creation: The Docker daemon proceeds to create the container with the requested privileged access and host mounts.
- Host Compromise: The attacker gains root-level access to the host system via the privileged container, enabling data exfiltration, persistence, or lateral movement.
The vulnerability is rooted in insufficient input validation and improper access control within the Docker daemon's API request processing, specifically related to how it interacts with AuthZ plugins and handles oversized data payloads.
Why This Matters
This vulnerability represents a critical threat to the integrity and confidentiality of systems running Docker. By allowing an attacker to bypass authorization controls, it effectively grants them a direct pathway to compromise the host operating system. This means sensitive data residing on the host, such as cloud credentials, SSH keys, configuration files, and proprietary information, becomes accessible.
The ability to create a privileged container with full host filesystem access is a game-changer for attackers. It transforms a potentially isolated containerized environment into a launchpad for complete system takeover. This can lead to significant operational disruptions, data breaches, and reputational damage for affected organizations. Furthermore, a compromised host can be used as a pivot point to launch further attacks against other systems within the network, escalating the impact of the initial breach.
The fact that this is an incomplete fix for a previous vulnerability underscores the importance of thorough security patching and regression testing. It highlights how seemingly minor oversights in security updates can reintroduce severe risks.
Defensive Takeaways
Organizations must prioritize patching their Docker Engine installations to version 29.3.1 or later to address CVE-2026-34040. For those unable to patch immediately, several mitigation strategies can reduce the attack surface:
- Limit Docker API Access: Implement strict network segmentation and access controls for the Docker API. Ensure only trusted users and services can connect, and avoid exposing the API directly to the internet.
- Run Docker in Rootless Mode: This significantly reduces the impact of privilege escalation. In rootless mode, the Docker daemon and its containers run as an unprivileged user on the host, limiting the blast radius even if a container is compromised.
- Review AuthZ Plugin Configuration: If using AuthZ plugins, assess their reliance on request body inspection. Consider alternative plugins or configurations that do not depend solely on this method for authorization decisions.
- Monitor for Suspicious Container Activity: Implement robust logging and monitoring for Docker events. Look for the creation of privileged containers, unexpected host filesystem mounts, and anomalous process behavior within containers.
Source
- Original Source: Zerosday News
- Related CVE: CVE-2024-41110
