EngageLab SDK Flaw Exposed 50M Android Users, Including 30M Crypto Wallets
Widespread Android SDK Flaw Threatened Millions of User Data
A critical security vulnerability discovered in a popular third-party Android software development kit (SDK) could have exposed sensitive data for over 50 million users. The flaw, present in the EngageLab SDK, specifically impacted a significant number of cryptocurrency wallet applications, potentially jeopardizing the private information of approximately 30 million users within that ecosystem.
The vulnerability allowed malicious applications on the same device to bypass Android's security mechanisms and access protected data. This broad reach underscores the inherent risks associated with the reliance on third-party code in modern application development. While the issue has since been patched, the incident highlights the cascading security implications of even seemingly minor flaws in widely adopted SDKs.
Technical Context
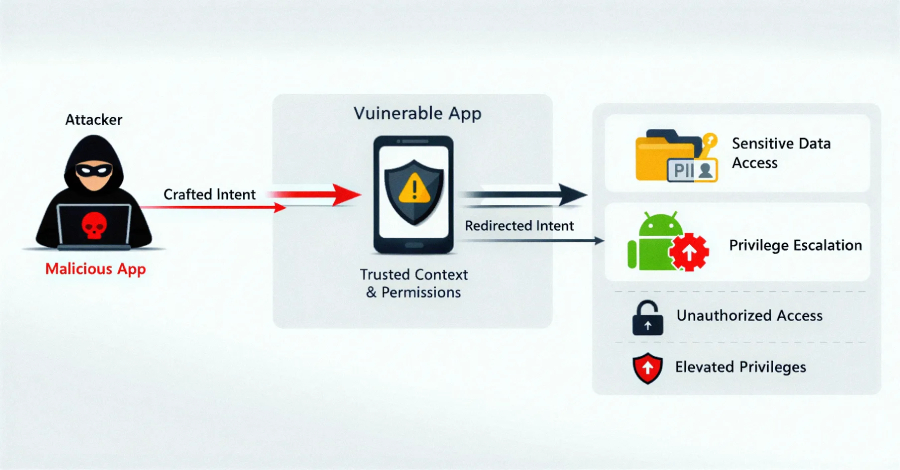
The vulnerability, identified as an intent redirection flaw in EngageLab SDK version 4.5.4, exploited how Android applications communicate with each other. Android's "Intents" are messaging objects used to trigger actions or share data between app components. In this case, an attacker could craft a malicious application that manipulates the intents sent by a legitimate app using the vulnerable SDK.
By leveraging the trusted context of the compromised app, an attacker could redirect these intents to gain unauthorized access to internal directories. This could lead to the exfiltration of sensitive data stored by the app, including potentially user credentials, private keys for cryptocurrency wallets, or other personally identifiable information. The attack vector would involve a malicious app installed on the user's device, which then exploits the EngageLab SDK's weakness in other applications.
Why This Matters
The sheer scale of the potential exposure, affecting over 50 million Android installations, makes this incident particularly concerning. The fact that a substantial portion of these were cryptocurrency wallet applications elevates the risk considerably, as compromised wallet data could lead to direct financial loss for users.
This case serves as a stark reminder of the complexities of the software supply chain. Developers often integrate numerous third-party SDKs to accelerate development and enhance functionality. However, vulnerabilities within these external components can propagate rapidly across a vast user base, creating widespread security risks that are difficult to contain. The opaque nature of some SDK integrations can also obscure potential security weaknesses until they are actively exploited or discovered.
Defensive Takeaways
Organizations integrating third-party SDKs should prioritize thorough vetting and continuous monitoring of their dependencies.
- Prompt Updates: Ensure all SDKs are updated to their latest stable versions, especially after security advisories are released.
- Dependency Auditing: Regularly audit the SDKs used in applications, assessing their security posture and the potential impact of any known vulnerabilities.
- Least Privilege Principle: Design applications to adhere to the principle of least privilege, limiting the data and permissions accessible by any single component, including integrated SDKs.
- Security Testing: Incorporate robust security testing, including dynamic and static analysis, to identify vulnerabilities within integrated third-party code.
- Incident Response Planning: Develop and practice incident response plans that specifically address the compromise of third-party components.
Source
This article is based on information initially reported by Zerosday News.
