Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
Source: The Hacker News
Published: Mon, 23 Mar 2026 10:55:00 GMT
Microsoft has warned of fresh campaigns that are capitalizing on the upcoming tax season in the U.S. to harvest credentials and deliver malware.
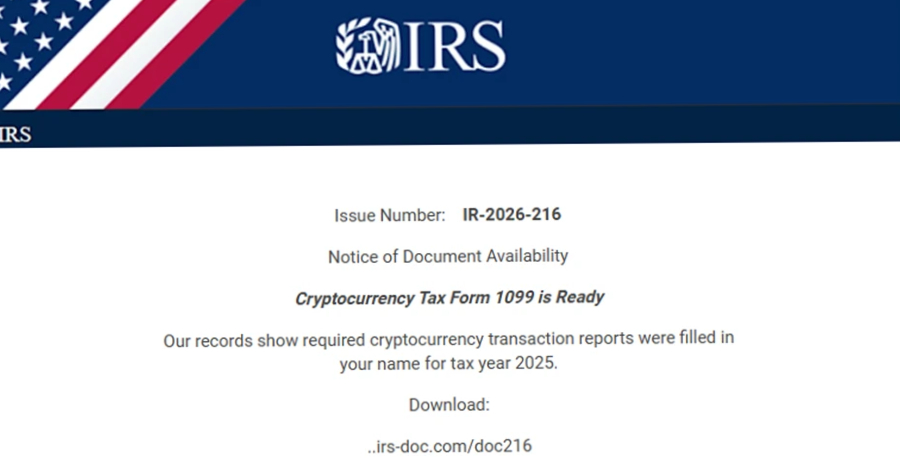
The email campaigns take advantage of the urgency and time-sensitive nature of emails to send phishing messages masquerading as refund notices, payroll forms, filing reminders, and requests from tax professionals to deceive recipients into opening malicious attachments, scanning QR code, or interacting with suspicious links.
"Many campaigns target individuals for personal and financial data theft, but others specifically target accountants and other professionals who handle sensitive documents, have access to financial data, and are accustomed to receiving tax-related emails during this period," the Microsoft Threat Intelligence and Microsoft Defender Security Research teams said in a report published last week.
While some of these efforts direct users to sketchy pages designed through Phishing-as-a-service (PhaaS) platforms, others result in the deployment of legitimate remote monitoring and management tools (RMMs), such as ConnectWise ScreenConnect, Datto, and SimpleHelp, enabling the attackers to gain persistent access to compromised devices.
The details of some of the campaigns are below -
Microsoft said it also observed a large-scale phishing campaign on February 10, 2026, in which more than 29,000 users across 10,000 organizations were affected. About 95% of the targets were located in the U.S., spanning industries like financial services (19%), technology and software (18%), and retail and consumer goods (15%).
"The emails impersonated the IRS, claiming that potentially irregular tax returns had been filed under the recipient's Electronic Filing Identification Number (EFIN). Recipients were instructed to review these returns by downloading a purportedly legitimate 'IRS Transcript Viewer,'" the tech giant said.
The emails, which were sent through Amazon Simple Email Service (SES), contained a "Download IRS Transcript View 5.1" button that, when clicked, redirected users to smartvault[.]im, a domain masquerading as SmartVault, a well-known document management and sharing platform.
The phishing site relied on Cloudflare to keep bots and automated scanners at bay, thus ensuring that only human users are served the main payload: a maliciously packaged ScreenConnect that grants the attackers remote access to their systems and facilitates data theft, credential harvesting, and further post‑exploitation activity.
To stay safe against these attacks, organizations are recommended to enforce 2FA on all users, implement conditional access policies, monitor and scan incoming emails and visited websites, and prevent users from accessing the malicious domains.
The development coincides with the discovery of several campaigns that have been found to drop remote access malware or conduct data theft -
The findings follow an uptick in RMM adoption by threat actors, with the abuse of such tools surging 277% year-over-year, according to a recent report published by Huntress.
"As these tools are used by legitimate IT departments, they are typically overlooked and considered 'trusted' in most corporate environments," Elastic Security Labs researchers Daniel Stepanic and Salim Bitam said. "Organizations must stay vigilant, auditing their environments for unauthorized RMM usage."
A practical deep dive into securing AI agents against real-world attack paths beyond the model itself.
See exactly where your controls stand against today’s threats—automated, accurate, approachable.
Source
Original report: https://thehackernews.com/2026/03/microsoft-warns-irs-phishing-hits-29000.html
