ZeroDay Cyber Feed
Explore fresh threat intelligence, zero-day vulnerabilities, and cyber news. Stay ahead of the curve with our real-time feed of the latest in cybersecurity.
Professional Course Tracks
Learn offensive security, network exploitation, red team operations, and real-world penetration testing techniques aligned with industry standards and hands-on vulnerability assessment practices.
Most detailed category with step-by-step breakdowns, realistic scenarios, and practical examples.
CVE posts are concise vulnerability summaries for fast awareness and prioritization.
Infrastructure assessment, exposure mapping, and internal attack-chain coverage for practical testing.
Follow CVE summaries for context, then move to Red-Team for deeper techniques and examples.

The popular HTTP client known as Axios has suffered a supply chain attack after two newly published versions of the npm package introduced a malicious dependency that delivers a trojan capable of targeting Windows, macOS
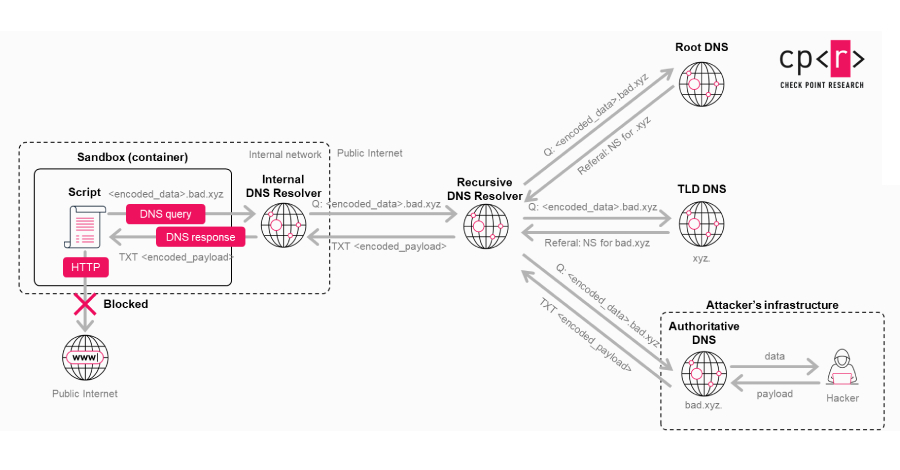
A previously unknown vulnerability in OpenAI ChatGPT allowed sensitive conversation data to be exfiltrated without user knowledge or consent, according to new findings from Check Point. "A single malicious prompt could t
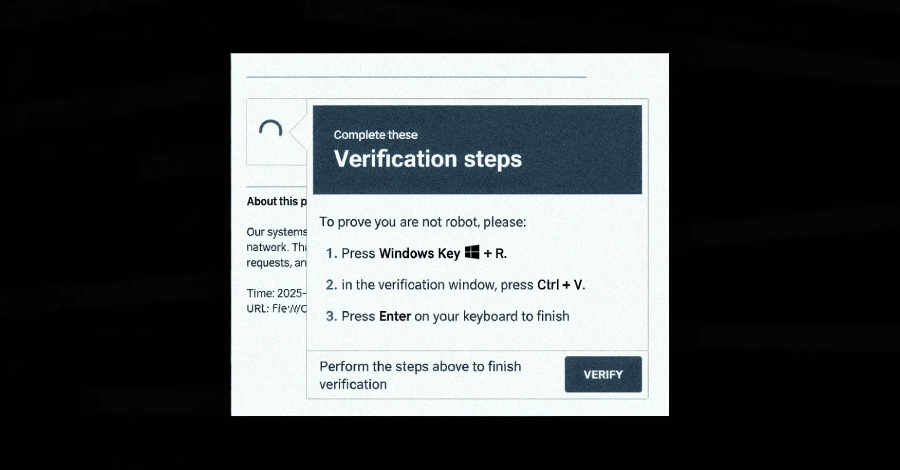
A new campaign has leveraged the ClickFix social engineering tactic as a way to distribute a previously undocumented malware loader referred to as DeepLoad . "It likely uses AI-assisted obfuscation and process injection

What is really slowing Tier 1 down: the threat itself or the process around it? In many SOCs, the biggest delays do not come from the threat alone. They come from fragmented workflows, manual triage steps, and limited vi