ZeroDay Cyber Feed
Explore fresh threat intelligence, zero-day vulnerabilities, and cyber news. Stay ahead of the curve with our real-time feed of the latest in cybersecurity.
Professional Course Tracks
Learn offensive security, network exploitation, red team operations, and real-world penetration testing techniques aligned with industry standards and hands-on vulnerability assessment practices.
Most detailed category with step-by-step breakdowns, realistic scenarios, and practical examples.
CVE posts are concise vulnerability summaries for fast awareness and prioritization.
Infrastructure assessment, exposure mapping, and internal attack-chain coverage for practical testing.
Follow CVE summaries for context, then move to Red-Team for deeper techniques and examples.
Cybersecurity researchers have disclosed a vulnerability in Anthropic's Claude Google Chrome Extension that could have been exploited to trigger malicious prompts simply by visiting a web page. The flaw "allowed any webs
Cybersecurity researchers have discovered a new payment skimmer that uses WebRTC data channels as a means to receive payloads and exfiltrate data, effectively bypassing security controls. "Instead of the usual HTTP reque
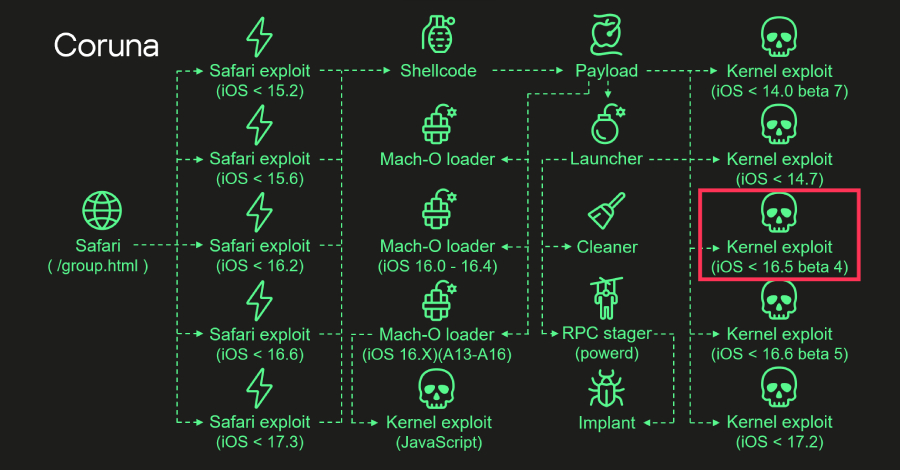
The kernel exploit for two security vulnerabilities used in the recently uncovered Apple iOS exploit kit known as Coruna is an updated version of the same exploit that was used in the Operation Triangulation campaign bac
![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks](/img/posts/news/webinar-stop-guessing-learn-to-validate-your-defenses-against-real-attacks.jpg)
Most teams have security tools in place. Alerts are firing, dashboards look clean, threat intel is flowing in. On the surface, everything feels under control. But one question usually stays unanswered: Would your defense