ZeroDay Cyber Feed
Explore fresh threat intelligence, zero-day vulnerabilities, and cyber news. Stay ahead of the curve with our real-time feed of the latest in cybersecurity.
Professional Course Tracks
Learn offensive security, network exploitation, red team operations, and real-world penetration testing techniques aligned with industry standards and hands-on vulnerability assessment practices.
Most detailed category with step-by-step breakdowns, realistic scenarios, and practical examples.
CVE posts are concise vulnerability summaries for fast awareness and prioritization.
Infrastructure assessment, exposure mapping, and internal attack-chain coverage for practical testing.
Follow CVE summaries for context, then move to Red-Team for deeper techniques and examples.
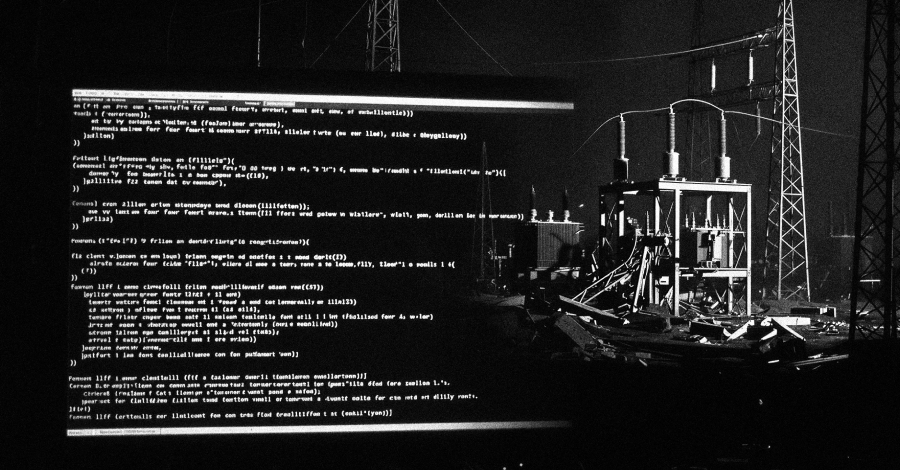
A newly identified data wiper, dubbed Lotus Wiper, has been employed in targeted attacks against Venezuela's energy and utilities infrastructure, leaving systems inoperable without any ransom demands. Published: 2026-04-

Federal agencies face strict deadlines to patch critical security flaws actively exploited by threat actors, as CISA adds new vulnerabilities to its Known Exploited Vulnerabilities catalog. Published: 2026-04-21 | Author

A sprawling botnet linked to the SystemBC proxy malware has revealed over 1,570 victims of the "The Gentlemen" ransomware-as-a-service (RaaS) operation, indicating a significantly larger scale of activity than previously

A newly disclosed suite of 22 security flaws, dubbed BRIDGE:BREAK, impacts thousands of Lantronix and Silex devices, potentially allowing attackers to seize control of connected industrial systems and manipulate critical