Chinese National Accused of Sophisticated Phishing Scheme Targeting U.S. Defense Technology
Chinese National Accused of Sophisticated Phishing Scheme Targeting U.S. Defense Technology
A multi-year spear-phishing operation, orchestrated by a Chinese national posing as a U.S. researcher, successfully infiltrated U.S. government agencies and research institutions to illicitly acquire sensitive defense software. The campaign, which ran for several years, highlights the evolving tactics of adversaries seeking to compromise intellectual property and advanced technological information.
Published: 2026-04-24 | Author: Patrick Mattos
The U.S. National Aeronautics and Space Administration's (NASA) Office of Inspector General (OIG) has detailed a sophisticated phishing scheme that exploited trust between researchers and collaborators. A Chinese national, identified as Song Wu, allegedly impersonated U.S. engineers for years, soliciting proprietary software and source code under the guise of professional collaboration. This operation not only targeted NASA but also extended to other government bodies, universities, and private companies, raising significant concerns about export control violations and the potential transfer of advanced technology.
The indictment against Song Wu, unsealed in September 2024, outlines a campaign spanning from January 2017 to December 2021. Wu, an engineer at the state-owned Aviation Industry Corporation of China (AVIC), is accused of conducting extensive reconnaissance to build rapport with targets before requesting specialized software. This software is critical for aerospace design and weapons development, including applications for advanced tactical missiles and aerodynamic assessments. The success of this scheme underscores the persistent threat of social engineering in cyber espionage.
Technical Context
The attack chain employed by Song Wu and his alleged co-conspirators relied heavily on social engineering and impersonation. Victims were led to believe they were sharing software with legitimate colleagues or collaborators. This trust was leveraged to solicit proprietary software and source code, likely through email exchanges. The objective was to gain access to modeling software used in critical defense sectors.
While specific technical details of the exfiltration methods are not fully disclosed, the campaign's success in obtaining sensitive defense technology suggests that victims may have inadvertently provided access to intellectual property that is subject to U.S. export control laws. The investigation noted that common indicators of such fraud include repetitive software requests without clear justification, unusual payment methods, and attempts to mask identity and evade shipping restrictions.
Impact and Risk
The primary impact of this operation is the potential compromise of sensitive U.S. defense technology, including software used in the development of advanced weaponry and aerospace systems. Organizations affected include NASA, the U.S. Air Force, Navy, Army, and the Federal Aviation Administration, alongside numerous universities and private sector firms. The risk level is high, as the acquired technology could provide adversaries with significant advantages in military and industrial applications.
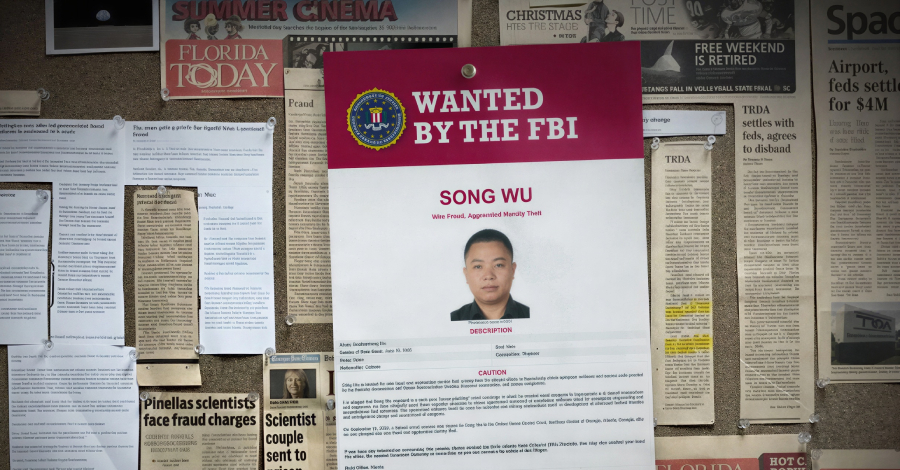
Song Wu faces serious charges, including wire fraud and aggravated identity theft, with potential prison sentences of up to 20 years for wire fraud and an additional two years for aggravated identity theft. His current whereabouts are unknown, as he remains at large. The U.S. Federal Bureau of Investigation (FBI) has placed him on its Most Wanted List, emphasizing the gravity of the national security implications.
Defensive Takeaways
Organizations must reinforce their security awareness training, particularly focusing on identifying and reporting suspicious communication patterns. Key indicators of phishing and export control fraud include:
- Unusual Software Requests: Be wary of repeated requests for the same software without clear justification or a legitimate business need.
- Suspicious Communication: Scrutinize emails that suggest unconventional payment methods, abrupt changes in payment terms, or attempts to mask sender identity.
- Impersonation Red Flags: Verify the identity of senders, especially when sensitive information or proprietary software is requested. Cross-reference requests through established communication channels.
- Export Control Awareness: Ensure personnel are educated on U.S. export control laws and the implications of sharing sensitive technology with foreign nationals or entities.
Implementing robust email filtering and security gateways can help detect and block malicious communications. Furthermore, establishing clear protocols for software sharing and intellectual property protection is crucial for mitigating such threats.
